Scalable awareness programmes with clear visibility into behaviour over time.

Cybersecurity, Nicht kategorisiert
Enterprise cybersecurity: Structures, strategies and best practices for corporations
Enterprise cybersecurity requires more than technology alone. Most security gaps today come from how people, processes and systems fail to work together in practice. This article explains how organisations can manage cybersecurity as an ongoing business function and embed it across the organisation through clear structures, defined responsibilities and practical day-to-day behaviours.
- Enterprise security vs cybersecurity
- Three core elements
- Training: what to consider
- Enterprise cybersecurity software
- KPIs for cybersecurity
- Trends
Overview: Enterprise Cybersecurity
- Enterprise cybersecurity depends on clear structures, not isolated measures.
- Technology, processes and security culture work best when they support each other.
- Effective awareness training helps employees recognise risks and respond with more confidence over time.
- Tools deliver more value when they are aligned with the wider security architecture and embedded in day-to-day processes.
- KPIs create visibility, support decision-making and help teams prepare for audits.
Enterprise security vs. cybersecurity: What companies need to know
Enterprise security describes the overall approach organisations take to protect their operations. It goes beyond cybersecurity. It includes governance, risk management, physical security and business continuity.
These elements need to work together across locations, cloud environments and supply chains. If they are managed separately, gaps appear between teams and systems.
Cybersecurity is one part of this broader structure. It focuses on protecting digital assets such as systems, data and identities. It also provides the technical controls that support detection, response and recovery.
Enterprise security architecture brings these elements together. It defines how controls, responsibilities and processes connect. This makes it easier to manage risk consistently across the organisation.
What makes enterprise environments special
Security requirements in large organisations are more complex than in smaller ones. Enterprise environments often combine technical complexity, distributed ownership and regulatory pressure at the same time.
Typical challenges at enterprise level include:
- Parallel systems, from on-premises infrastructure to multi-cloud, hybrid cloud and software-as-a-service (SaaS) applications.
- Legacy environments and technical debt, often made worse by acquisitions, regional variations or inconsistent standards across business units.
- Unclear ownership between the Chief Information Security Officer (CISO), Chief Information Officer (CIO), business functions and risk teams. This often leads to different views of risk, compliance and audit readiness.
- Broad supply chains with many external partners, which increase the attack surface.
- Operational technology (OT) and Internet of Things (IoT) environments, where cybersecurity measures need to be balanced with availability and safety requirements.
- Security incidents that need to be managed across time zones, languages and legal jurisdictions.
This is why enterprise cybersecurity needs a clear strategy. It must bring together technical diversity, organisational complexity and global requirements. It also needs to stay manageable in practice, so teams can maintain visibility and control over time.
Overview of industry-specific requirements
Cybersecurity requirements vary by industry. They are shaped by regulation, operational risk and system dependencies.
- Finance: High requirements for confidentiality, integrity and regulatory compliance. Controls need to support auditability and risk reporting.
- Public sector: Protection of critical infrastructure under strict legal and procurement constraints. Implementation is often slower due to governance processes.
- Energy supply / KRITIS: Availability is the priority. Segmentation, monitoring and tested contingency plans are essential to maintain operations.
- Global companies: Different jurisdictions and data localisation requirements increase complexity. Consistent identity and access models help maintain control across regions.
These differences affect how security programmes are designed and operated. A one-size-fits-all approach rarely works at enterprise level.
From theory to practice
A strategic framework helps translate cybersecurity goals into daily operations. It provides reusable structures that teams can apply consistently.
This often includes architectural principles, minimum standards and maturity models. These define how controls are implemented and how progress is measured over time.
Many organisations base this on established frameworks such as TOGAF or the NIST Cybersecurity Framework. These frameworks provide guidance on governance, architecture and risk management.
The challenge is not choosing a framework. It is applying it in a way that fits existing systems, teams and operational constraints.
Three core elements of enterprise cybersecurity
A holistic enterprise cybersecurity strategy rests on three connected elements: technology and infrastructure, processes and governance, and people and security culture. Each element plays a different role. Real resilience only develops when they work together in practice.
Technology provides visibility, protection and response capabilities. Processes and governance create structure, accountability and consistency. People and security culture shape how securely decisions are made in day-to-day work.
If one element is weak, the whole approach becomes harder to sustain. Isolated initiatives may look effective on paper, but they rarely hold up over time.
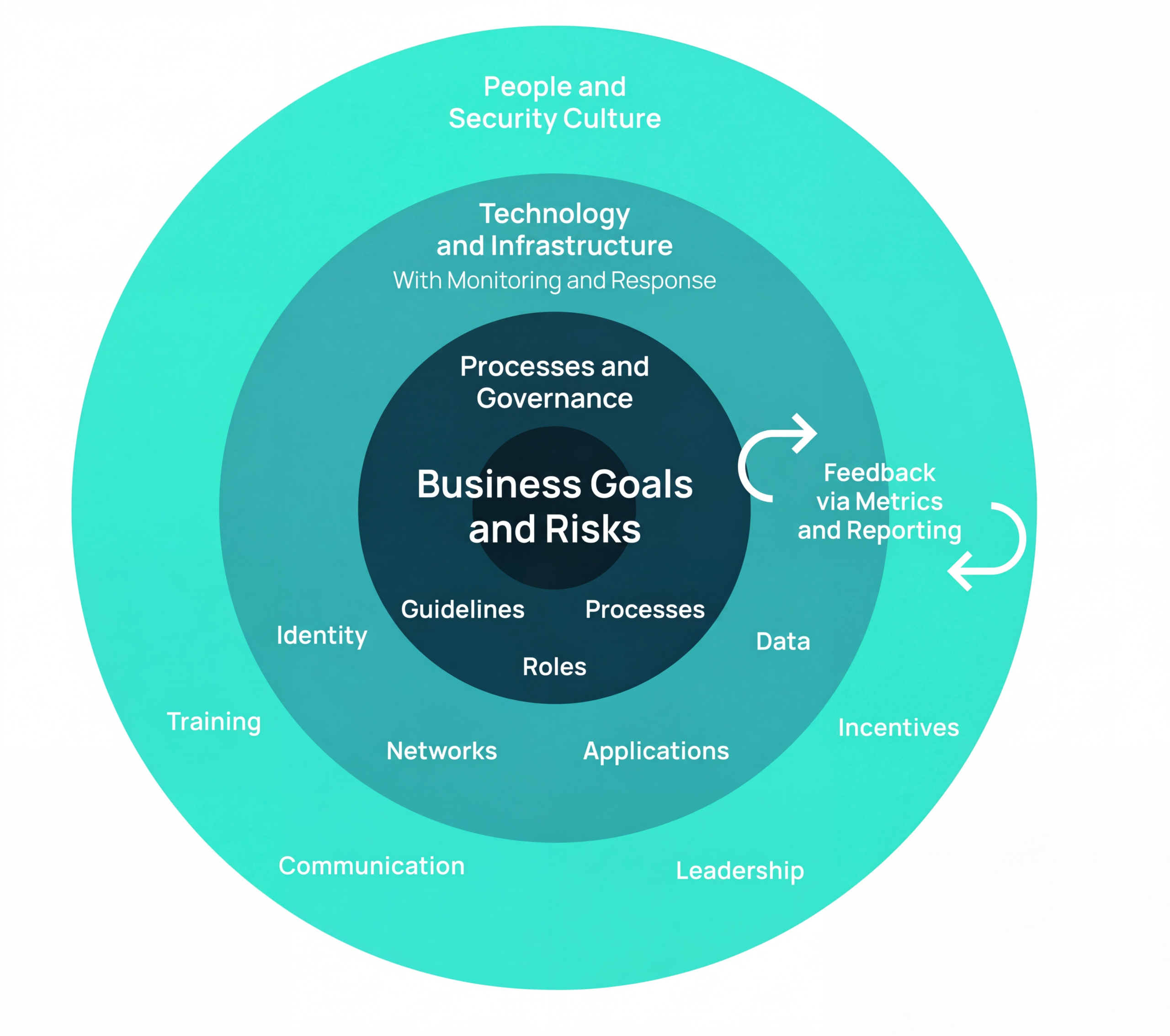
Processes and governance
Strategic guidelines only matter when they are translated into clear responsibilities and repeatable processes. This includes defined roles, practical policies, and structured approaches to risk, exceptions and escalation.
Mature operational and crisis management processes create transparency and traceability. They also give teams a stronger basis for decision-making, regardless of location or business area.
Technology and infrastructure
Technology and infrastructure form the technical foundation of enterprise cybersecurity. This often includes identity-centred cybersecurity, network segmentation and secure cloud baselines.
These foundations are supported by access controls, system hardening and continuous monitoring. Integration matters just as much as coverage. Without shared standards, tools can multiply quickly. That creates tool sprawl, reduces visibility and slows down response.
People and security culture
Technology and processes only create value when they are applied in everyday work. A strong security culture helps employees make safer decisions across the organisation, from leadership teams to specialist functions.
Regular training, clear communication and positive reinforcement all play a role. Platforms such as SoSafe support this through awareness training, phishing simulations and behaviour-based learning paths that fit into existing processes and systems. Managers also play an important role because they help set expectations and model secure behaviour.
The most common imbalance
Many organisations invest heavily in technical controls first. Processes and security culture often develop more slowly.
That imbalance weakens the impact of technical measures. Even with strong tooling, risk stays higher when ownership is unclear, behaviours are inconsistent or teams are not supported in day-to-day decisions.
Designing effective enterprise cybersecurity training
Standard training is not enough for large organisations. Effective enterprise cybersecurity training needs to scale across roles, regions and regulatory contexts. It also needs to fit into existing governance, processes and systems. That is what makes impact easier to measure over time.
Acceptance begins with the user experience
Training needs to be clear, relevant and easy to access. Microlearning formats, plain language and realistic contexts improve engagement and support learning. Role-specific learning paths also help employees see why the content matters in their day-to-day work.
Demonstrating compliance reliably
Large organisations need verifiable training records. These records should reflect roles, policies and assigned responsibilities. Recertifiable modules and audit trails make internal reviews and external audits easier to manage.
Up to date, localised and effective
Global training programmes need regular updates. They also need to reflect legal, linguistic and cultural differences across regions. Threat patterns do not look the same everywhere, so training should adapt to local risk profiles instead of relying on one fixed global approach.
Seamless integration into systems and processes
Training has more impact when it is integrated into existing systems and workflows. This can include learning management systems, human resources platforms, and identity or collaboration tools. Interfaces support automation, more consistent reporting and closer links to phishing simulations.
Leadership as a cultural amplifier
Security culture is shaped by what managers say and do. Regular communication and positive incentives help reinforce secure behaviour over time.Solutions such as the SoSafe platform support this by delivering behaviour-based, risk-based training that can be adapted to different roles, regions and threat contexts. Open interfaces and reporting features also help organisations connect training to existing system landscapes and track progress more clearly.
Reduce human-related risk with measurable training
Enterprise cybersecurity: integrating software effectively
A consistent software stack is a core part of enterprise cybersecurity. The tools in that stack should support clearly defined use cases and fit into a wider cybersecurity architecture. This is what allows organisations to connect data flows, support operational processes and assign responsibilities clearly.
Without that structure, tools can become fragmented. Visibility drops, handovers slow down and response becomes harder to coordinate.
Selection based on architecture and integration
Enterprise cybersecurity software needs to offer more than standalone functionality. It should support the organisation’s architecture, integrate with existing systems and scale in day-to-day operations. Compatibility with models such as zero trust also matters.
Tools deliver lasting value when they fit into established processes and reporting structures. If they do not, complexity rises and visibility falls.
Overview of core technical categories
A typical enterprise stack includes:
- Identity and access management (IAM/PAM)
- Endpoint detection and response or extended detection and response (EDR/XDR)
- Security information and event management (SIEM) with user and entity behaviour analytics (UEBA)
- Secure service edge solutions, including secure access service edge (SASE) and cloud access security broker (CASB)
- External attack surface management (EASM)
This stack is often supported by additional components. These can include secrets and key management, vulnerability and patch management, email and web security, and cloud-native controls such as cloud security posture management (CSPM) and cloud workload protection platforms (CWPP).
The human factor as an integral part
Technical measures are more effective when they are supported by the human factor. That is why awareness training, anti-phishing measures and policy enablement also belong in an enterprise cybersecurity programme.
Platforms such as SoSafe support this through behaviour-based training, phishing simulations and reporting capabilities that fit into existing system landscapes. This helps organisations connect human risk activities to wider reporting, management updates and audit preparation.
Consolidation or best-of-breed?
Many organisations face a practical choice. They can consolidate tools to reduce complexity, or they can use specialised best-of-breed solutions for specific needs.
Consolidation can simplify operations and integration. It may also require trade-offs in functionality. Best-of-breed tools can offer more depth, but they often increase maintenance effort and interface complexity.
In practice, many organisations combine both approaches. A clear reference architecture helps make that workable. It should define interfaces, telemetry standards and minimum requirements for integration and reporting.
Operating models with clear control
Whether security tools are run in-house, managed by a provider or operated jointly, responsibilities need to be clear. Reliable service levels also matter. The same is true for a realistic exit strategy.
This is what supports long-term control and adaptability. Without it, dependence grows and operational change becomes harder to manage.
KPIs for enterprise cybersecurity: measure, control, report
Key performance indicators help make progress in enterprise cybersecurity visible. They support prioritisation and enable structured reporting to management and auditors.
To be useful, KPIs need clear definitions and consistent data sources. Responsibilities should also be defined, so ownership is clear.
It is helpful to group KPIs into three categories: operational, strategic and compliance-related. This makes reporting easier to structure and reduces confusion between technical metrics and business-level outcomes.
Operational KPIs at a glance
| KPI | Definition | Measurement method / source | Responsible |
| Incident Frequency | Number of security incidents within a defined period | Incident response or ticketing system. Incidents should be deduplicated by use case | Security operations (SecOps) |
| Mean Time to Detect (MTTD) | Time between the initial event and detection | Security information and event management (SIEM) or extended detection and response (XDR) telemetry, combined with incident response timestamps | Security operations (SecOps) |
| Mean Time to Respond/Recover (MTTR) | Time from detection to containment or recovery | Incident response playbooks, configuration management database (CMDB) data and change records | Security operations (SecOps) / IT operations (IT Ops) |
| Patch Compliance Rate | Percentage of systems patched within the defined deadline | Vulnerability management and CMDB data, measured against system criticality | IT operations (IT Ops) |
Strategic enterprise cybersecurity KPIs
| KPI | Definition | Measurement method / source | Responsible |
| Phishing Click-Through Rate (CTR) | Percentage of users who click on simulated phishing emails | Awareness platform data, segmented by role, region or campaign | Awareness Lead |
| Training completion and retention | Training completion rate and evidence of knowledge retention over time | Learning management system (LMS) and assessment data, segmented by role and region | Learning and development (L&D) / awareness |
| MFA Coverage (Identity) | Percentage of identities protected by multifactor authentication (MFA) | Identity and access management (IAM) or identity provider (IdP) reports, measured against the defined identity scope | IAM |
| Zero-Trust Control Coverage | Share of defined zero trust controls that are implemented and active | Architecture reviews, configuration scans and control validation checks | Architecture / governance, risk and compliance (GRC) |
Compliance indicators at a glance
| KPI | Definition | Measurement method / source | Responsible |
| Audit Readiness Score | Degree of alignment with audit-relevant controls | Control catalogue, such as ISO or NIST, with supporting verification records | Governance, risk and compliance (GRC) |
| Policy Adoption Rate | Share of employees or teams with confirmed policy acceptance | Learning management system (LMS) and human resources (HR) data, supported by spot checks where needed | GRC / HR |
| SLA Adherence (Security Services) | Degree to which security-related service-level agreements (SLAs) are met | Service reports and operational-level agreement (OLA) data | Security operations (SecOps) / IT operations (IT Ops) |
| Third-Party Risk Status | Current risk status of external partners within the third-party risk process | Third-party risk management (TPRM) tool, contract data and risk assessments | Vendor Risk |
Reporting formats and frequency
Operational metrics should usually be reviewed monthly in SecOps management. This helps teams spot changes early and respond before issues build up.
Strategic KPIs are better suited to quarterly management reviews. At that level, the focus is less on daily activity and more on trends, priorities and investment decisions.
Compliance metrics should follow audit cycles and regulatory deadlines. They also need to align with the existing enterprise cybersecurity architecture and the frameworks the organisation uses.
Consistency and structure
Consistency matters as much as coverage. A central glossary, shared baselines for each domain, and segmentation by role, region and platform make KPIs easier to compare over time.
A central data source also helps reduce confusion. It limits silos, inconsistencies and double counting. For enterprise cybersecurity, that kind of structure is essential if reporting is meant to scale.
Current trends in enterprise cybersecurity
The threat landscape is constantly changing – and with it the requirements for effective enterprise cybersecurity. New technologies, regulatory requirements and the increasing complexity of global infrastructures make forward-looking action essential.
AI-assisted attacks
Generative AI improves the quality and scalability of phishing campaigns, deepfakes and automated reconnaissance. Deception is becoming more sophisticated – especially in social engineering.
Automated campaigns and crimeware-as-a-service
Attacks are organised on an industrial scale. Toolchains and marketplaces for initial access shorten the path from identification to exploitation to monetisation.
New requirements from regulations and directives
NIS2 (Who is affected?) increases the requirements for governance, reporting channels and evidence. At the same time, the development of structured AI governance is gaining importance, including in the context of enterprise cybersecurity.
Cloud-native environments and supply chain risks
Dependence on SaaS, PaaS and infrastructure partners is growing. Third-party risk management and transparency through Software Bill of Materials (SBOM) are becoming key components.
OT and IoT in enterprise architectures
The increasing interconnection of IT and OT systems requires segmented cybersecurity architectures that take into account safety objectives, operational processes and the availability of critical systems. IoT components increase the interface between IT and OT, making clear zones and interface controls indispensable.
Resilient cybersecurity structures rely on technology, processes and behaviour working together. With clear priorities and measurable goals, this becomes reliable business practice.






















