Train your teams in a measurable way and meet NIST requirements.

NIST Cybersecurity Framework 2.0: Governance, Maturity and Practical Implementation
The NIST Cybersecurity Framework 2.0 expands its scope to all organisations and introduces Governance as the sixth core function – your practical guide.
Contents
- What is NIST?
- NIST 1.1 vs. 2.0
- 6 Core Functions
- Implementing NIST 2.0
- Measuring the Maturity Levels
- Certification
- NIST 2.0 vs. ISO 27001
Overview: NIST 2.0
- The NIST Cybersecurity Framework 2.0 introduces Govern as the sixth core function and strengthens governance aspects
- NIST CSF 2.0 is aimed at all organisations – not just critical infrastructures
- Awareness training and phishing simulations meet key Protect and Detect requirements
- Implementation Tiers from Partial to Adaptive enable maturity measurement
- NIST Cybersecurity Framework 2.0 and ISO 27001 are ideal complements as Enterprise Security Frameworks for technical and certifiable security
What is NIST?
The National Institute of Standards and Technology (NIST) is a non-regulatory research agency of the U.S. Department of Commerce. What NIST develops – from atomic clocks and encryption standards to cyber security guidelines – serves as a global reference. The National Vulnerability Database (NVD) records security vulnerabilities based on the Security Content Automation Protocol (SCAP). For companies, this means they can keep track of vulnerabilities and automate large parts of the monitoring process.
The SP 800-207 guideline defines the NIST Zero Trust Architecture – and it has fundamentally revolutionised security concepts. The principle behind it: “Never trust, always verify”. Instead of relying on a one-time login, it constantly verifies who is accessing what. Identity Management is at its core, combined with strict access rules and seamless monitoring.
In 2014, the NIST Cybersecurity Framework was created following a presidential Executive Order to protect critical infrastructures. On 26 February 2024, NIST 2.0 was released – the most significant revision in ten years. The scope was massively expanded, and a completely new governance function, Govern, was added.
NIST CSF 1.1 vs. 2.0: The most important changes
From NIST CSF 1.1 to NIST CSF 2.0, a lot has changed both structurally and in terms of content. The NIST Cybersecurity Framework has become more future-proof and practical:
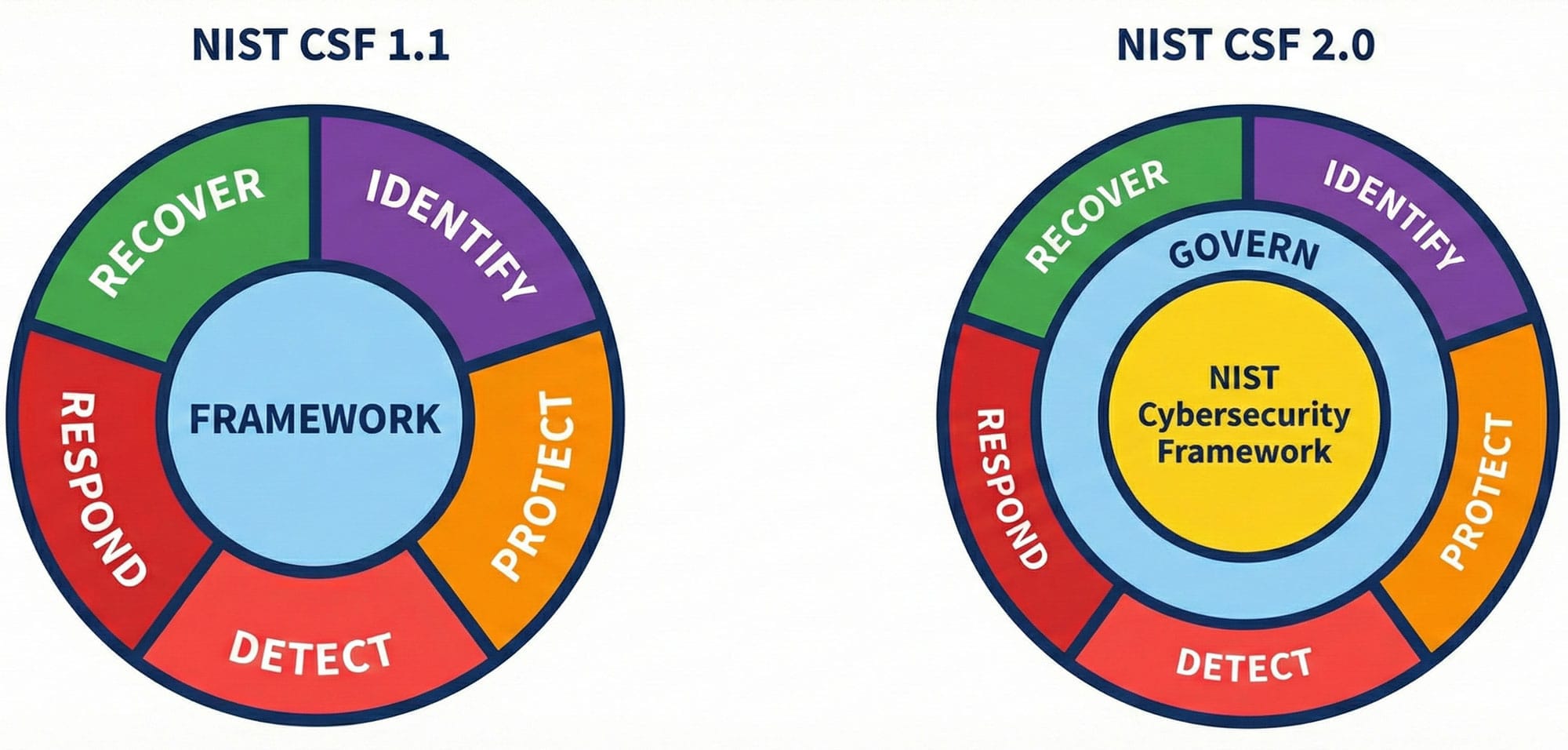
Key Changes in NIST CSF 2.0
- Sixth Core Function “Govern”: What was distributed across all functions in NIST CSF 1.1 is now bundled centrally in NIST 2.0 – governance is now at the centre
- Expanded target audience: The NIST Cybersecurity Framework 2.0 no longer addresses only critical infrastructures, but all organisations from non-profits to large corporations
- Supply Chain Risk Management: Supplier relationships, risk prioritisation and contractual security requirements are brought sharply into focus
- Secure Software Development: DevSecOps and Software Supply Chain Security are given significantly more weight in NIST 2.0
- Simplified language: Security Controls are described in a more understandable and practical way in the NIST Cybersecurity Framework 2.0
- Better integration: NIST CSF 2.0 harmonises seamlessly with NIST SP 800-161 (Cybersecurity Supply Chain) and SP 800-218 (Secure Software Development)
The visual difference is immediately noticeable: NIST CSF 1.1 showed five functions in a cycle on the same level. In NIST 2.0, Govern is central and influences all other functions.
The 6 Core Functions of the NIST Cybersecurity Framework 2.0
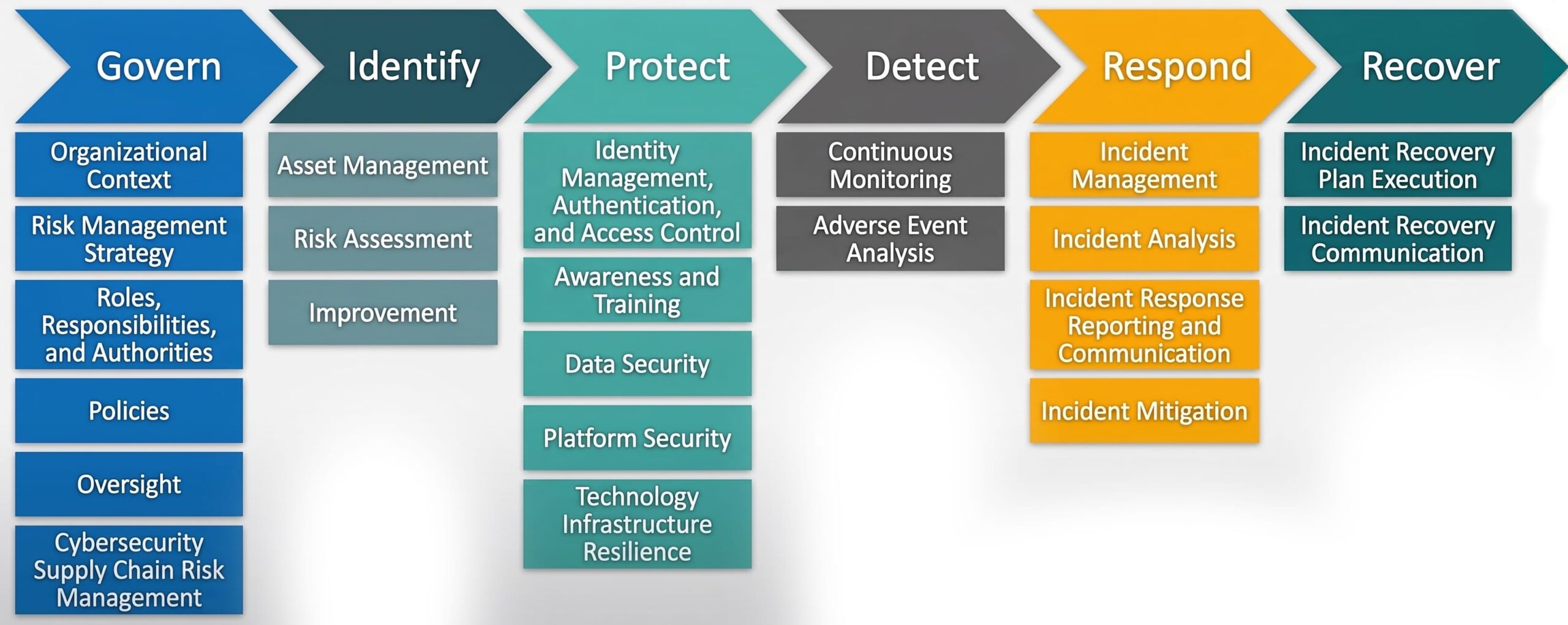
Govern (GV)
Governance creates the strategic foundation for the entire cyber security risk management process in the NIST Cybersecurity Framework 2.0. This includes the risk management strategy, role definitions, responsibilities and monitoring of the security strategy. Crucially: Cyber security is integrated into the Enterprise Risk Management (ERM) strategy – cyber risks are on a par with financial and operational risks. The Human Risk Management platform quantifies human risks and supports data-based management decisions.
Identify (ID)
Before you can manage risks in NIST 2.0, you need to know which assets exist. Data, hardware, software, systems, employees, suppliers – and their associated risks. This function lays the foundation for risk-based prioritisation, consistent with the Govern strategy of the NIST Cybersecurity Framework. Cyber security awareness training makes employees aware of threats and helps with asset and risk identification.
Protect (PR)
Protective measures in NIST CSF 2.0 reduce the likelihood and impact of negative security events. Identity Management, Authentication, Access Control, Data Security, Platform Security – the list is long. Awareness training is indispensable in this function of the NIST Cybersecurity Framework 2.0 – it turns employees into the strongest line of defence against social engineering. In addition, there is the resilience of the tech infrastructure that keeps your critical business processes running.
Detect (DE)
There is no such thing as one hundred percent security, even with the best protective measures. This is precisely why the Detect function of NIST 2.0 is needed: It detects anomalies, indicators of compromise and potential threats in a timely manner. With continuous monitoring and Adverse Event Analysis, you lay the foundation for successful Incident Response in the NIST Cybersecurity Framework. Phishing simulations realistically test the vigilance of your teams and reveal weaknesses.
Respond (RS)
As soon as an incident is detected, the Respond function of NIST CSF 2.0 comes into play. It governs how you specifically handle incidents: from the first management step, through analysis and damage limitation, to reporting and communication. That’s why you need to clearly define in advance who needs to be informed internally and externally about which incidents – this includes stakeholders as well as public authorities. The faster your teams react and the closer the collaboration, the lower the impact.
Recover (RC)
After an incident, the focus is on recovery. The Recover function of the NIST Cybersecurity Framework 2.0 includes Incident Recovery Plan Execution and Incident Recovery Communication. Plan and test recovery in parallel with response – this is the only way to be able to act in an emergency. Goal: minimal impact and a quick return to normal operation.
Awareness training for NIST 2.0
Implementing NIST 2.0: Step-by-step to adaptive cyber security risk management
The implementation of the NIST Cybersecurity Framework 2.0 follows four clear steps:
Step 1: Conduct a status quo analysis
Create a Current Profile that maps your current security status in NIST CSF 2.0. Which outcomes of the six Core Functions of the NIST Cybersecurity Framework have you already achieved? Which controls are implemented, and where are the gaps? This stocktake is the basis for everything that follows in NIST 2.0.
Step 2: Define a Target Profile
The Target Profile defines your desired outcomes – aligned with the strategic goals and risk management requirements of the NIST Cybersecurity Framework 2.0. Take into account the risk appetite and risk tolerance thresholds from Govern. This way you know where your organisation should be in the medium term.
Step 3: Prioritise measures
The gap analysis between the Current and Target Profiles shows specific areas for action in NIST 2.0. Prioritise according to risk impact, available resources and feasibility. Document this as a Risk Register, Risk Detail Report or Plan of Action and Milestones (POA&M).
Step 4: Create a roadmap with clear responsibilities
Your Action Plan needs defined responsibilities, resources, milestones and deadlines for the NIST implementation. Each measure is assigned a responsible person, and a monitoring system continuously tracks progress. Update the Current Profile regularly after implementation and adjust the Target Profile if necessary.
Implementation Tiers: The path to Adaptive Security
NIST CSF 2.0 distinguishes four maturity levels:
Tier 1 – Partial: Security processes in the NIST Cybersecurity Framework? Ad hoc or minimal. Your risk management is reactive, your organisation is not prepared for attacks.
Tier 2 – Risk-Informed: Security policies exist, but the implementation of NIST 2.0 is not yet complete in your company. You know the risks in theory, but (so far) you have no consistent assessment method.
Tier 3 – Repeatable: The security practices of NIST CSF 2.0 are firmly anchored in your organisation. They are documented and regularly reviewed. Both risk management and data security follow clear, standardised procedures in your company.
Tier 4 – Adaptive: Security in the NIST Cybersecurity Framework 2.0 permeates your entire organisation, is continuously monitored and reacts flexibly to new threats. You don’t just carry out risk assessments when necessary, but permanently – and cyber risks are given the same priority as financial or operational risks.
Adaptive cyber security means that your security measures evolve with the threat landscape. Modern Human Risk platforms provide real-time data on the behaviour and risk level of your employees – so you can manage measures dynamically.
Achieve adaptive security
From Tier 1 to Tier 4 with measurable and continuous SoSafe training.
How to measure the NIST CSF 2.0 Maturity Levels
NIST CSF 2.0 makes cyber security maturity measurable – through Profiles and Implementation Tiers. Current Profiles show the as-is state, Target Profiles the to-be state in relation to the Core Outcomes of the NIST Cybersecurity Framework. From Partial to Adaptive, the four tiers in NIST 2.0 risk management become increasingly sophisticated and stricter.
How do organisations assess their maturity in NIST CSF 2.0? With Key Performance Indicators (KPIs) that show how well controls are working, for example patch speed, the success rate of phishing simulations or the average response time to incidents. In addition, there are Key Risk Indicators (KRIs), which make risks visible at an early stage. Discuss these figures regularly with your executives – after all, good decisions need a reliable data basis.When should you aim for a higher tier in the NIST Cybersecurity Framework? When your risk situation worsens, regulatory requirements force you to, or the cost-benefit analysis is right.
However, the long-term goal remains Tier 4 \”Adaptive\” in NIST 2.0: Security that grows with the threat landscape and makes your organisation permanently more resilient. What does that mean in concrete terms? Adaptive organisations constantly keep an eye on their systems, regularly update their policies with best practices and integrate security data into all areas of the company. A measurable level of maturity shows CISOs the ROI of their investments in the NIST Cybersecurity Framework – budgets can thus be justified on a data-driven basis.
Certification: How NIST CSF certification works
Unlike ISO 27001, the NIST Cybersecurity Framework does not require formal certification or external audits. The NIST CSF is voluntary, a guide for individual adaptation. NIST itself does not issue certificates to organisations.
However, third-party providers do offer certifications for professionals who implement or advise on NIST CSF 2.0. \”NIST CSF 2.0 Lead Implementer\”, for example, qualifies individuals to develop, implement and manage security programmes according to the NIST Cybersecurity Framework. Such certificates confirm individual competence – not an organisation’s compliance with NIST 2.0.
You can use the NIST CSF freely without ever undergoing an audit. You document the implementation of the NIST Cybersecurity Framework 2.0 via self-assessment, maturity tiers and organisational profiles – formal proof is optional, unless contracts or regulations explicitly require it.
NIST Cybersecurity Framework vs. ISO 27001: Differences and synergies
The NIST Cybersecurity Framework and ISO 27001 pursue the same goal, namely managing security risks, but they go about it in different ways.
| Criterion | NIST CSF 2.0 | ISO 27001 |
| Type | Flexible framework, guidance | Prescriptive standard, ISMS |
| Certification | No official certification | Formal certification by accredited bodies |
| Costs | Available free of charge | Audit and certification fees |
| Approach | Outcome-oriented, flexibly adaptable | Requirements-based, mandatory requirements |
| Proof of Compliance | Self-assessment, Profiles, Tiers | External audits, certificate |
| International Recognition | Primarily USA, increasingly global | Globally recognised |
The two standards complement each other perfectly. Many organisations use NIST CSF 2.0 to build a technical basis and then formalise these controls with ISO 27001 to create a certifiable management system. Common principles: risk-based approach, senior management support, continuous improvement.
CISOs benefit from both: The NIST Cybersecurity Framework for flexible control implementation and risk communication at the executive level, ISO 27001 for formal certification, international recognition and a structured ISMS. Many map NIST 2.0 controls to ISO 27001 requirements – so you can serve both standards efficiently.
Note: This article does not constitute legal advice. It is for general information purposes only and does not replace an individual legal review. For binding information on NIST CSF 2.0, please contact qualified legal advisors or the relevant authorities.



















