
Human Firewall: the Key to Cyber Resilience
Technology alone is not enough to protect you. Instead, people are the first line of defence against cyberattacks. A strong Human Firewall detects attacks early and can therefore prevent damage.
Contents
- Meaning: What is a Human Firewall?
- Why do you need one?
- Best-practice examples
- Prerequisites
- Building a Human Firewall
- Measuring success
Overview: Human Firewall
- Employees recognise attacks and limit damage through security-conscious behaviour
- Awareness training, courses, phishing simulations and simple reporting channels embed security in everyday work
- Management acts as a role model, ensures clear responsibilities and an open error culture
- Click and reporting rates in the Security Dashboard make the progress of the Human Firewall visible
- Human behaviour effectively complements technical protective measures
Meaning: What is a Human Firewall?
The term ‘Human Firewall’ (which translates as ‘menschliche Firewall’ in German) describes the security-conscious behaviour and competencies of employees in dealing with cyber threats. They detect attacks early, react appropriately and report incidents reliably. The Human Firewall complements technical protective measures with human judgement. It takes effect when the first signs of suspicion arise – and ensures that they are passed on quickly and correctly.
The definition of a Human Firewall also includes the term ‘human malware’. This refers to behaviours such as curiosity, time pressure or excessive helpfulness, which attackers specifically exploit in social engineering. A strong Human Firewall counteracts this with clear responsibilities, established reporting channels and heightened security awareness.
Regulatory requirements such as the Cyber Resilience Act also bring the human factor into focus. They demand secure processes along the entire product life cycle. Training, clear procedures and comprehensible reporting are therefore gaining further relevance.
Why do you need a Human Firewall?
Over a third of users click on malicious content in phishing emails – and just under two-fifths of them continue to interact with the content. At the same time, data from the SoSafe Human Risk Review shows that after twelve months of awareness training, the reporting rate for suspicious activities tripled. A well-established Human Firewall therefore measurably reduces misconduct and improves responsiveness.
Human Firewall examples from practice
Real-life incidents show how crucial employee behaviour is – and which routines help. The following Human Firewall examples illustrate how security-conscious actions prevent attacks or reduce their impact.
Case 1: Loss of control during a penetration test
As part of a red teaming test, external security experts managed to gain physical access to the company premises through a fake job interview. Without being checked, they reached internal offices and found unprotected network access points there. This gave them access to internal systems, they escalated privileges and were able to remotely control central components. They also managed to take company car keys with them when leaving the building. You can find an article on this at heise (in German) and further background information in a conversation with the affected Team Leader Infrastructure & Operations in our Human-Firewall-Podcast:
How could the Human Firewall have worked (better)?
Reporting unusual admin rights early, asking questions via defined channels and using clear escalation paths. This is how lateral movements can be stopped before they cause damage.
Case 2: MGM Resorts – Ransomware after helpdesk vishing
Attackers posed as internal IT staff on the phone and tricked the helpdesk into resetting sensitive access data. This gave them access to privileged accounts and they prepared to deploy ransomware. Within a very short time, central booking and payment systems were offline and operations in several hotels came to a standstill. The perpetrator group ‘Scattered Spider’ used psychological pressure and targeted deception in the style of classic social engineering techniques.
How could the Human Firewall have worked (better)?
Calling back verified numbers, mandatory identity checks and fixed reset policies protect helpdesk processes from social engineering.
Case 3: Continental – LockBit attack via an insecure download
An employee allegedly downloaded an unofficial tool from the internet that contained malicious code. This gave attackers access to internal systems, they moved laterally through the network and exfiltrated large amounts of data. The attack initially went undetected and only became public when LockBit posted stolen data on the darknet. Continental responded with internal investigations and involved the authorities. Der Spiegel (in German) was one of the publications that reported on it.
How could the Human Firewall have worked (better)?
Recognise risks, report suspicious files, insist on secure tools. A prominent report button and clear guidelines support reporting behaviour.
Prerequisites for a functioning Human Firewall
A Human Firewall is created where security is a part of everyday life. It is based on clear processes, tangible support from managers and a training programme that translates knowledge into behaviour. Simple reporting channels, an open error culture and continuous empowerment are crucial. Only when these elements work together does the Human Firewall effectively contribute to cybersecurity.
Leadership and clear responsibilities
Managers lead by example with secure behaviour. Responsibilities are clearly distributed and documented in a RACI matrix. Sponsorship and budget ensure implementation.
Secure and simple reporting channels
Low-threshold channels such as a report button, hotline or chat, as well as a clearly communicated email address, make reporting easier. The path from reporting to ticket creation is designed to be completed in under a minute. Protection for the reporting person is guaranteed by a no-blame principle and transparent feedback.
Mandatory guidelines and training
Clear policies on IT use, communication, password security, software and third-party providers create orientation. Mandatory modules are supplemented by role-based in-depth sessions – short, practical and effective. Microlearning, in-app notifications and simulations with debriefing promote sustainable behaviour and thus a functioning Human Firewall.
Standardised processes and suitable tools
Standardised reporting processes with ticket autofill, query playbooks for the helpdesk and first-level support, as well as clearly defined escalation SLAs, ensure fast reactions. Visible KPIs in the dashboard and security briefings during on- and off-boarding – including rights checks and shadow IT checks – round off the process.
Building a Human Firewall: Programme and training
An effective Human Firewall is created through coordinated measures that are integrated into the daily work routine. The goal is a clear process: from detecting suspicious signals to reporting and providing feedback to the person who reported it.
Core components
- Cybersecurity awareness training with personalised microlearning and storytelling
- Phishing simulations with instant feedback
- Phishing Report Button as an Outlook add-in for one-click reporting
- Human Risk Dashboard with click, reporting and behavioural metrics
- AI chatbot ‘Sofie’ for queries – directly in Teams or Slack
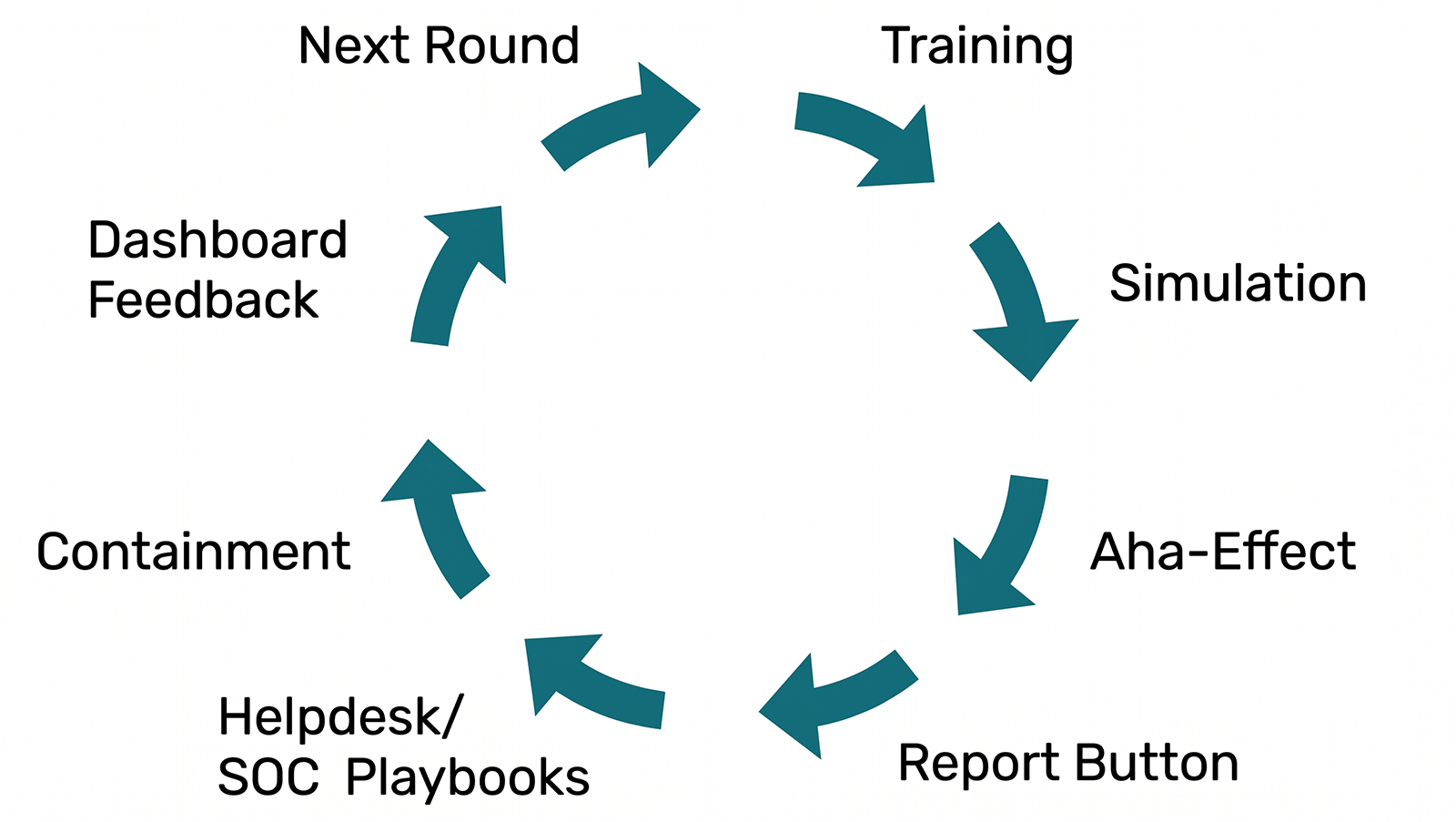
Process model of the Human Firewall
SoSafe introduction in three phases
Phase 1: Start and basic configuration (days 1 and 2)
Activate the platform, connect SSO and the user directory. Roll out the report button, define reporting targets. Unlock the first microlearning modules and prepare basic scenarios. Configure the dashboard.
Phase 2: Pilot and fine-tuning (from day 3)
Start the pilot group, run a simulation with instant feedback. Activate the ‘Sofie’ chatbot, provide query prompts. Test the helpdesk and SOC playbook, train callback processes.
Phase 3: Go-live and consolidation
Rollout to all target groups. Deliver microlearning regularly, repeat simulations. Establish the report button, regularly evaluate dashboards with management. Incorporate lessons learned into policies.
Measuring success and continuous improvement
Only what is measured can be controlled. Choose a few, understandable key figures – easy to collect and relevant for teams and management.
Reduce the phishing click rate
The click rate across several campaigns shows that fewer and fewer people are reacting to simulated phishing emails because the training is effective.
Increase the reporting rate
The reporting rate indicates how many employees actively report suspicious content, for example via the reporting button. A high reporting rate shows attentiveness and the ability to act.
Measure training participation and knowledge level
Completion rates and knowledge checks reflect whether content has been understood. Combine these values with simulation results.
Observe security behaviour in everyday work
Is two-factor authentication being used? Are unusual requests being reported? Spot checks and internal feedback help to realistically assess behaviour.
Make key figures visible
A monthly report with trends on click, reporting and training metrics is often sufficient. Measures can be derived from this on a quarterly basis. Embed these KPIs under ‘Enterprise Cyber Security‘ and reflect the results in the SoSafe Dashboard.
Ultimately, what counts is that people form the first line of defence every day and make security tangible with clear routines. Start with small, measurable steps and develop the Human Firewall step by step into a living part of your work culture.



















