Discover how SoSafe’s Human Risk Management Dashboard can help make aspects of human risk easier to assess and track within your enterprise architecture.

TOGAF framework: structuring enterprise architecture
The TOGAF framework gives IT architects a common language. This article looks at what the TOGAF framework is for, where it tends to be useful, and whether certification is worth considering.
Contents
- What is TOGAF?
- Enterprise Architecture Suitability
- Domains
- TOGAF ADM (Architecture Development Method)
- Certification
- TOGAF vs. other frameworks
What is TOGAF? A practical introduction
The TOGAF framework, short for The Open Group Architecture Framework, is a widely used method for planning, shaping and governing enterprise architecture. Maintained by The Open Group, the TOGAF framework gives organisations a shared structure for connecting IT decisions with business direction, using common terminology and established TOGAF architecture principles. For readers looking for a straightforward explanation of what TOGAF is, TOGAF offers a way to organise architecture work so it can be developed, reviewed and adapted over time, rather than a set of fixed technical answers.
The TOGAF framework originated in 1995 from the US Department of Defense’s Technical Architecture Framework for Information Management (TAFIM). Since then, it has been continuously developed by The Open Group’s Architecture Forum. Today, The Open Group includes more than 900 member organisations worldwide.
At its core, the TOGAF framework addresses three practical questions: where an organisation stands today, where it wants to go, and how it can get there. The TOGAF framework outlines how architectures across different areas of the business can be developed, managed and refined in a systematic way. Used consistently, the TOGAF framework can help reduce duplication, improve coordination between IT and business teams, and support more transparent strategic decision-making.
TOGAF 10: what’s new?
In April 2022, The Open Group released TOGAF 10, the most substantial update to the standard so far. Three changes are especially relevant for CISOs and IT leaders:
- Modular structure: The previously monolithic standard has been broken into standalone modules. This allows organisations to apply the parts of the TOGAF framework that are most relevant to their context without adopting the entire framework at once.
- Guidance for agile delivery and transformation: TOGAF 10 includes expanded guidance for agile organisations and digital transformation initiatives. This makes the TOGAF framework more practical in environments where architecture work needs to support faster delivery and ongoing change.
- More practical implementation guidance: The newer version adds more applied, hands-on material alongside the conceptual model. As a result, the TOGAF framework is more accessible for smaller teams and for professionals using it for the first time.
TOGAF suitability: opportunities and limitations in enterprise use
The TOGAF framework is usually most useful in large organisations with many departments, overlapping IT initiatives and system landscapes that have developed over time. In that kind of environment, architecture decisions are easily made in isolation: one team optimises locally, another works to a different model, and security requirements are applied unevenly across the estate. Used well, the TOGAF framework can give those organisations a clearer basis for coordination and a more joined-up approach to TOGAF enterprise architecture.
Smaller organisations and highly agile teams often reach a different conclusion. Too much structure can slow delivery, and too many artefacts can become shelfware. If the TOGAF framework is treated as a box-ticking exercise, it often produces exactly that. Used more selectively as a practical thinking tool, however, the TOGAF framework can still provide real value without overloading delivery teams.
For CISOs, one question is especially important: where in the enterprise architecture are security requirements anchored in a consistent and enforceable way? Two elements of TOGAF architecture are particularly relevant here.
Architecture content framework (ACF)
The Architecture Content Framework defines which artefacts are created in an enterprise architecture initiative and how those artefacts relate to one another. It covers the metamodel, building blocks, and deliverables that give architectural work its structure. For CISOs, this matters directly: security requirements, risk assessments, and compliance obligations can be embedded as recognised architectural artefacts instead of remaining isolated documents in separate organisational silos. When security is built into the TOGAF framework through the ACF, it becomes easier to ensure that it informs every major architecture decision. In this sense, the ACF is a core part of effective TOGAF architecture.
Enterprise continuum
The Enterprise Continuum is a classification model for architecture and solution artefacts, ranging from generic reference models to organisation-specific implementations. It helps teams develop existing architectures more systematically and makes reusable assets easier to identify. For IT leaders, this has a practical advantage: it creates a clearer link between strategic vision and operational delivery. Security architecture patterns can also be documented within the continuum as reusable assets and applied across future initiatives, which strengthens consistency within the TOGAF framework.
SoSafe’s Human Risk Management Dashboard can be integrated into a TOGAF framework as an operational component, helping organisations assess and monitor human risk more consistently at the point where strategic architecture and day-to-day security management intersect.
Making human risks visible
TOGAF domains: an overview of the four architectural layers
The TOGAF framework organises enterprise architecture into four clearly defined layers that together describe an organisation’s full IT landscape. These TOGAF domains provide the structural foundation for the Architecture Development Method and for architecture decisions across the business. In practice, the four layers are often grouped under the acronym BDAT: Business, Data, Application and Technology. Within the TOGAF framework, each domain addresses a distinct part of the enterprise while remaining closely connected to the others, which is what gives TOGAF architecture its coherence.
TOGAF business architecture
TOGAF business architecture is the starting point for any enterprise architecture initiative. It defines the organisation’s business strategy, structures, capabilities, processes and governance model. Within the TOGAF framework, this layer is especially important for CISOs because security requirements need to be tied to broader business priorities. A sound understanding of which capabilities and processes matter most to the business makes it easier to decide where controls are needed first and where security spending is likely to have the most practical effect.
TOGAF data architecture
TOGAF data architecture defines what data exists across the organisation, how it is structured, where it is stored and how it moves between systems. In the TOGAF framework, this domain creates an important basis for data protection, compliance and access management. In environments shaped by requirements such as the GDPR or NIS2, well-documented data architecture can support more consistent governance and clearer accountability around information flows.
TOGAF application architecture
TOGAF application architecture describes the application landscape: which systems are in use, how they interact and which business functions they support. In the TOGAF framework, this domain helps security leaders identify attack surfaces, understand dependencies and place controls where systems connect. If application architecture is missing or outdated, weaknesses in interfaces, ownership or system relationships may be harder to detect.
TOGAF technology architecture
TOGAF technology architecture covers the physical and logical infrastructure that underpins the rest of the estate, including networks, servers, cloud environments, middleware and security components. As part of the TOGAF framework, this domain defines the technical base on which all other architectural layers depend. For IT leaders, it can provide a clearer picture of technical maturity and highlight areas where security investment may have the greatest operational impact.
TOGAF ADM: the eight phases of architecture development
The TOGAF Architecture Development Method is the core process within the TOGAF framework. Often referred to as TOGAF ADM, it defines how enterprise architecture is developed, implemented, governed and continuously refined. The TOGAF framework uses this method to give architecture work a repeatable structure rather than treating it as a one-off design exercise. Because the process is iterative, the TOGAF framework supports continuous improvement instead of ending after a single cycle.
The process starts with a preparatory phase and a central requirements management function that remains active across all stages. From there, the TOGAF framework moves through phases A to H:
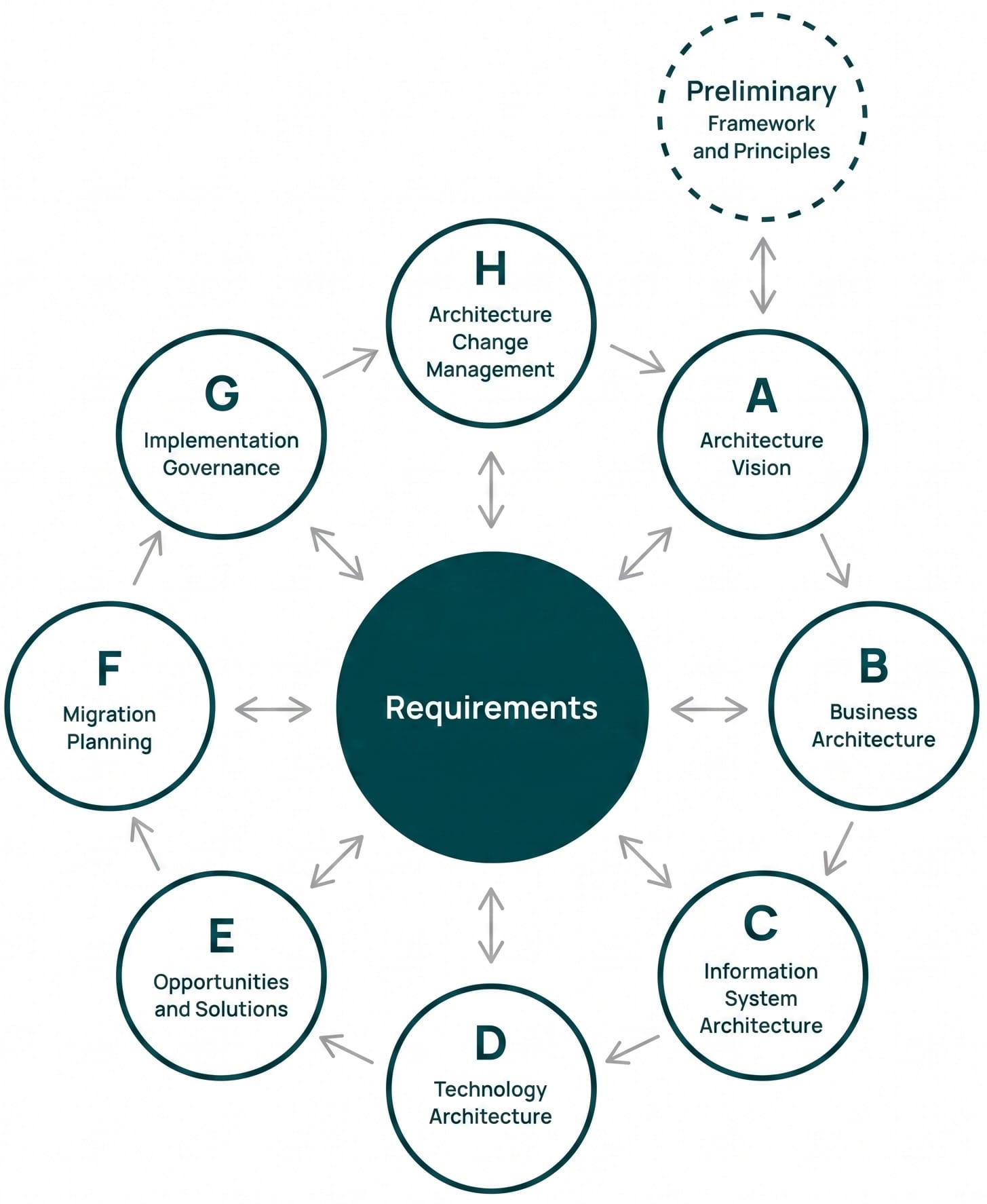
In day-to-day work, the TOGAF framework is rarely followed as a strict sequence from beginning to end. Teams extending an existing architecture may join the cycle midway, while others under delivery pressure may merge phases or work at a lighter level of detail. The method is designed to allow that kind of adaptation, which is one reason it remains workable in practice.
From architecture to implementation
SoSafe’s Human Risk Management Dashboard helps make the human factor in your IT architecture more visible and easier to manage.
TOGAF certification: costs, levels, and benefits
The Open Group offers two certification levels. Level 1 covers the fundamentals, including terminology, core concepts and the structure of the TOGAF framework. Level 2 focuses more on practical use. Candidates are expected to work through scenarios, make architecture judgements and show that they can apply the framework beyond theory. That makes TOGAF certification particularly relevant for enterprise architects, IT leaders and consultants who need more than a general overview.
The exams can be booked separately or taken together. On The Open Group’s published fee schedule, Part 1 and Part 2 are listed at USD 405 each, while the combined exam is shown at USD 610. The final cost of TOGAF certification may still end up higher once course fees are included, since authorised training providers set their own prices.
Is TOGAF certification worthwhile for security teams?
For security specialists in narrowly defined operational roles, TOGAF certification is not always essential. For CISOs, security architects and others who work across governance, architecture and risk, the picture looks different. In those roles, a working knowledge of the TOGAF framework can be useful because it helps security concerns enter broader architecture discussions earlier.
Whether the qualification is worthwhile depends largely on the role. For professionals who mainly focus on technical operations, the cost of TOGAF certification may outweigh the immediate benefit. For those shaping enterprise-wide security strategy or operating at the intersection of architecture and compliance, the framework can provide useful structural context. TOGAF is not a substitute for standards such as ISO/IEC 27001, but it can support the architectural groundwork that helps those requirements fit more effectively into the wider organisation.
TOGAF vs. other frameworks: the governance perspective
The TOGAF framework is not a competitor to frameworks such as ISO/IEC 27001, NIST, or COBIT. Instead, it operates at a broader level and can serve as a governance layer that helps define how and where other standards are applied within the enterprise architecture. The comparison below highlights the different roles these frameworks play:
| Framework | Primary focus | Relationship to TOGAF |
| TOGAF | Enterprise architecture, overarching IT governance | Overarching management framework |
| ISO/IEC 27001 | Information Security Management System (ISMS) | Embedded into the wider architecture through TOGAF |
| NIST CSF | Cybersecurity risk management and response | Operational security framework within a broader TOGAF governance model |
| COBIT | IT governance and management, process maturity | Complements TOGAF at the management and control level |
| SABSA | Risk-based security architecture | Complementary to TOGAF, with a specific focus on security architecture |
| Zachman | Classification framework for architecture artefacts | Conceptually related, but not a process model |
| ArchiMate | Modelling language for enterprise architecture | Often used alongside TOGAF as a notation language |
When the TOGAF framework is treated less as a rigid rulebook and more as a point of orientation, it can help keep security, compliance and business goals better aligned over time.



















