
DDoS Attacks
What is a DDoS attack?
Distributed Denial-of-Service (DDoS) attacks operate like an unruly mob of cars on a freeway, causing digital traffic jams of epic proportion. Imagine this: Hundreds, or even thousands of cars, flooding all lanes and causing a standstill, not allowing any other vehicle to pass through. That’s the essence of a DDoS attack – an avalanche of bogus traffic requests sent by hackers to a server or network, rendering websites temporarily or permanently unavailable for legitimate users.
But DDoS attacks aren’t a mere nuisance: They are a genuine threat. Just as a massive traffic jam can prevent emergency services from reaching their destination, a DDoS attack can stop critical data from getting through, halt operations, and lead to significant financial losses. The threat is real and growing: DDoS attacks saw a 74% surge from 2021 to 2022, with large corporations like Microsoft confronting an average of 1,435 DDoS attacks daily. Fortunately, when the appropriate preventative and mitigation measures are in place, DDoS attacks can be successfully blocked, as Google proved last year when it was hit by one of the largest DDoS to date.

How does a DDoS attack work?
In the vast interconnected digital landscape, any system connected to the internet may be a target for DDoS attackers. To launch a DDoS attack, cybercriminals rely on a legion of computers, known as botnets. These are previously hijacked computers that form a digital battalion commanded by hackers with a single destructive aim – to overwhelm target servers with an avalanche of requests. Since servers are built to handle only a limited number of requests within a given time, when this flood exceeds its capacity, it must deny access to incoming users. This business disruption can prevent customers from accessing websites for hours, days, or even weeks, which may result in significant financial losses.
DDoS attacks vary significantly in duration. As stated by Microsoft, a sizable 89% of these digital attacks in 2022 lasted less than one hour. This time frame, fleeting as it may seem, provides ample opportunity for severe damage – enough to shut down resources and block legitimate traffic. Interestingly, many cybercriminals actually lean toward these short, sharp strikes. They consume fewer resources and overwhelm the system enough to require a reboot. When the system comes back online, there is usually a rush of users trying to connect, which can result in a secondary internal traffic surge. This additional load can further stress the system, extending the disruption period.
DoS vs. DDoS attacks: What’s the difference?
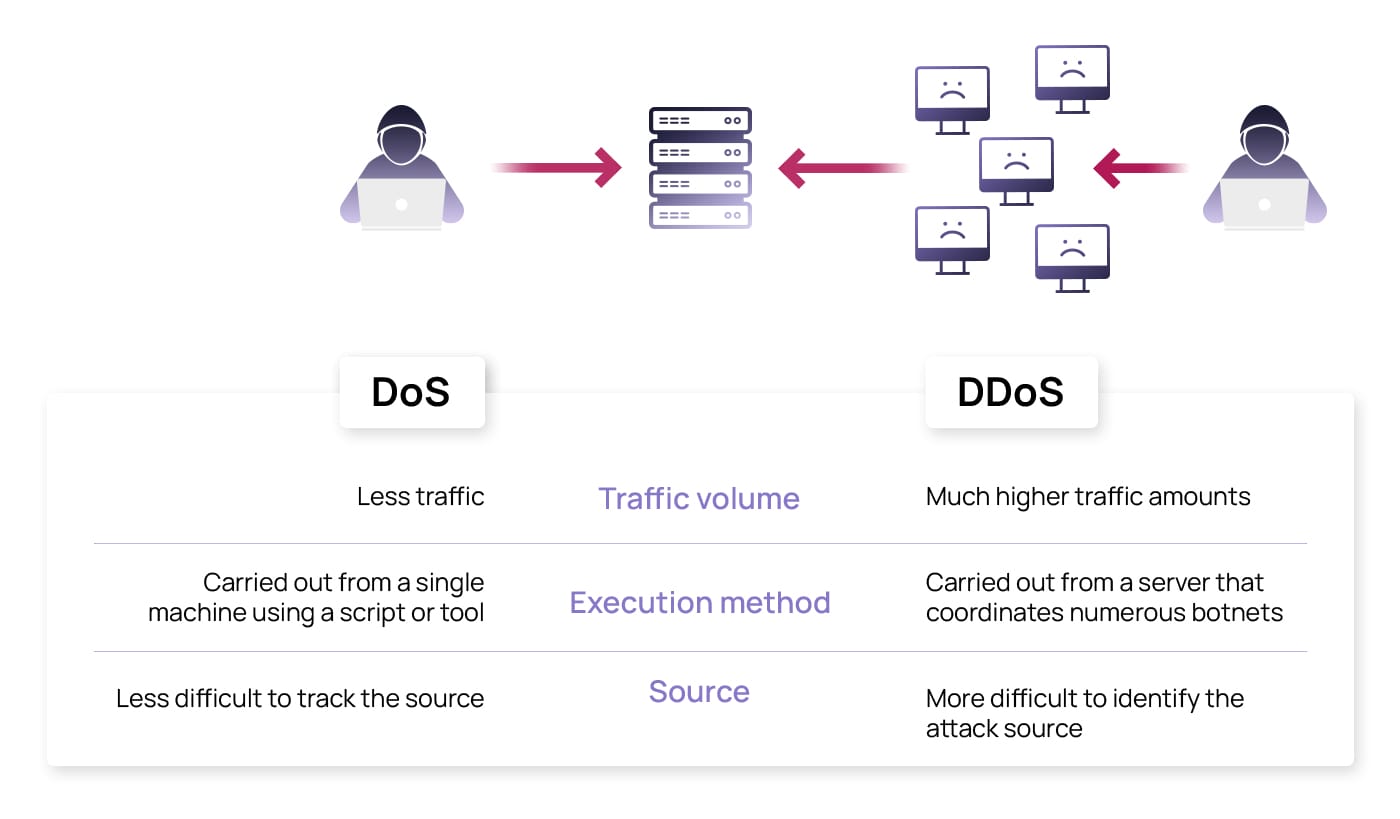
Distributed denial-of-service attacks fall under the broader category of denial-of-service (DoS) attacks. At the heart of a basic DoS attack, you have a single hacker who uses one internet connection to bombard a server with a flood of fraudulent requests, trying to exploit any vulnerabilities it finds.
Now, take this scenario and kick it up several notches, and you’ll find yourself face-to-face with a distributed denial-of-service (DDoS) attack. This isn’t just a single hacker anymore: thousands or even millions of connected infected computers controlled by hackers to achieve the end goal. The difference is dramatic. Whereas a DoS attack can be troublesome, a DDoS attack is a cyber onslaught. The sheer volume of devices involved makes it far harder to identify the attack source and to effectively fight against it. It’s not just a case of dealing with a troublesome hacker but rather confronting a well-coordinated, widescale threat.
What is the purpose of a DDoS attack?
DDoS attackers aim to disrupt normal web traffic to interrupt communication and services. While this may initially appear an act of pure vandalism, there is often an underlying motive behind these attacks, such as the infliction of financial losses and potential damage to a business’ reputation. In these attacks, hackers or even rival companies seek to capitalize on the diverted traffic resulting from the targeted organisation’s compromised online presence.
DDoS can also be combined with other tactics to amplify their consequences. In some sophisticated attacks, hackers threaten or initiate a distributed denial-of-service campaign and demand a ransom be paid to stop the attack, thus combining two of the most destructive attacks: ransomware and DDoS. Between the costly downtime and potential for additional cyberattacks, DDoS threats are serious concerns for modern businesses and something all employees should be aware of.
Types of DDoS attacks
In cyber security, DDoS attacks come in different forms. To understand them better, let’s move from the car metaphor and imagine a library operating smoothly. Its system functions effectively with a normal flow of visitors, but suddenly, an unusual influx of people disrupts that tranquility. This disruption mirrors the interruption a DDoS attack can inflict on a website’s server. There are three types of DDoS attacks or ways in which calm may be disturbed in our library: volume-based, protocol, and application-layer attacks.
Volume-based or volumetric attacks
A volumetric attack is like a large group of people suddenly entering the library, each grabbing as many books as they can carry and occupying all the reading areas. The library becomes overcrowded, making it difficult for regular visitors to find a place to sit or locate the books they need. This scenario is like a volumetric DDoS attack, where a massive amount of data is sent to the target, overwhelming its capacity to process the incoming traffic.
Protocol attacks
Public libraries rely on a computer system to help visitors locate and check out books. Protocol attacks are like someone exploiting a weakness in the library’s computer system, causing it to malfunction and leaving visitors unable to find or check out books. In a protocol attack, hackers exploit vulnerabilities in the target’s network protocols, leading to confusion and resource exhaustion.
Application-layer attacks
Imagine the library has a self-checkout system for borrowing books. An application-layer attack is like a group of people repeatedly using the self-checkout machines without actually borrowing any books, causing the machines to slow down and making it difficult for regular visitors to check out new reading materials. In an application-layer attack, rather than disrupting the infrastructure, the attacker targets security gaps and vulnerabilities in app software by sending malicious requests to the target applications or websites, consuming resources and preventing legitimate users from accessing the services.
How to identify a DDoS attack
One reason these attacks are so treacherous is their disguise. Originating from legitimate users’ infected computers, it becomes challenging to separate botnets from normal traffic. To complicate it further, the botnets involved are usually spread across the globe so that security experts cannot pinpoint a specific location and block all the suspicious traffic coming from it.
Detecting DDoS attacks is not always easy, but catching them early can significantly mitigate the severity of the consequences. To increase the chances of timely detection, look for these signs:
- Unusual spike in traffic volume
- Slow loading or unresponsive site
- Network connection problems
- Different traffic patterns than usual
- Spikes in server errors and resource usage
- IP address makes a high volume of requests in a short timeframe
- 503 server error indicating service outage
If any of these observations apply to your network, it’s worth investigating further and potentially deploying DDoS attack mitigation resources to prevent any additional disruption.
DDoS in action: A look at real cases
DDoS attacks can lead to ransomware threats, loss of critical services, reputational damage, and high remediation costs. Many organisations have discovered the hard way just how damaging a DDoS attack can be. Let’s look closer at real DDoS cases and how they negatively impact organisations worldwide.

Geopolitical DDoS attacks
In the current complex cyber threat landscape, DDoS attacks often serve as invisible artillery launched across the internet amid brewing political conflicts. A case in point occurred in August 2022, right before a visit from the U.S. House Speaker to Taiwan. In an unmistakable show of cyber power, DDoS attacks rained down on the Taiwanese government, resulting in significant outages. The targets were not random – they struck at the very heart of Taiwanese governance and communication: the President’s office, National Defense Ministry, Foreign Affairs Ministry, and the international airport.
A similar strategy was deployed against Israel’s Health Ministry website in July 2022, this time with a calculated focus on international visitors who found themselves blocked from accessing the site. Fast forward to March 2023, and the cyber battleground expanded to Australia, with university websites caught in the crosshairs of a DDoS campaign. Behind this attack were the threat actors Killnet and Anonymous Sudan. The fallout was substantial: Eight universities, eight hospitals, and ten airport websites were thrown into disarray.
DDoS attacks on tech giants
Major tech companies are another common target for DDoS attacks, as they hold a vast amount of data and are highly visible in today’s digital world. One of the largest examples of a DDoS attack against tech companies is the Amazon Web Services (AWS) attack in February 2020. 2.3 terabits of data per second flooded into the servers as hackers used compromised CLDAP servers to their advantage. Amazon successfully mitigated the attack before it could cause serious damage, although it became one of the largest DDoS attacks on record.
Another prominent example is a DDoS campaign launched against Google in June 2022. Luckily for the world’s leading search engine, the company’s IT infrastructure successfully blocked the attack, despite peaking at 46 million requests per second. The attempted attack involved over 5,000 devices in 132 countries over 30 minutes, receiving approximately the same amount of requests Wikipedia gets each day.
DDoS-for-hire: Digital sabotage at everyone’s fingertips
“DDoS-for-hire” refers to a marketplace where individuals or groups can pay a third party to orchestrate a DDoS attack against a chosen target. This space effectively turns cyber onslaughts into items for sale, empowering anyone to mastermind an attack with just a few clicks. In essence, it’s a marketplace for digital chaos, making disruption a readily available service.
Global authorities are acutely aware of this escalating threat and are now turning the script to combat hackers on their own turf. An interesting example of this comes from the UK’s National Crime Agency (NCA), which has recently established a website that ostensibly offers DDoS services but is, in fact, a sting operation aimed at catching cybercriminals looking for these illegal services.
Other authorities are also fighting the threat: The U.S. Justice Department has recently issued an alert about DDoS-for-hire domains, also called stressor or booter services. Over 50 domains have been seized as of mid-2023, although the FBI regularly monitors this threat as some cybercriminals register new domains to continue selling DDoS services.
Can you prevent DDoS attacks?
In the fast-paced and evolving landscape of cyber threats, the methods for mitigating and preventing DDoS attacks must also progress. The key to preventing DDoS attacks is a multi-layered approach that can be applied to different attack types. By putting in place a comprehensive set of protective measures that work in tandem to detect and mitigate DDoS attacks, we increase the chances of maintaining a secure network environment.
The first layer of defence should involve measures like rate limiting, IP filtering, and geo-blocking. Rate limiting can help control traffic and fend off attacks that aim to exhaust system resources. IP filtering can be used to block traffic from suspicious IP addresses, while geo-blocking can help exclude traffic from specific geographic locations known for originating attacks.
Intrusion detection systems (IDS) and intrusion prevention systems (IPS) form the next layer. These systems work by continuously monitoring network traffic, identifying suspicious patterns that could indicate a DDoS attack, and taking action to prevent or minimize damage. Additionally, deploying web application firewalls can help protect against more sophisticated application-layer attacks by scrutinizing incoming traffic for malicious patterns.
Having a robust incident response plan forms the last crucial layer of defence. This involves planning for the worst-case scenario where a DDoS attack breaches your defences. An effective plan will guide your response to minimize disruption, protect assets, and recover normal operations as quickly as possible. Regular testing and updating the incident response plan is also necessary to ensure it remains effective against current threats.
It’s important to remember that each method contributes to the overall protection of your network, but they cannot provide comprehensive protection when used in isolation.
DDoS attack protection myths
Understanding DDoS attacks involves learning about technical processes that may be hard for non-experts to understand. Adding to the challenge, the nature and strategies of these attacks are continuously evolving, turning yesterday’s facts into today’s outdated information. We collected some of the most persistent myths surrounding DDoS attacks over the years to shed some light and debunk common misconceptions.
Myth #1: DDoS attacks are annoying and disruptive but not actually dangerous
DDoS attacks cost $218K on average just for remediation expenses. Attacks involving ransomware are even more expensive. The misconception that DDoS attacks are annoying but not harmful comes from the idea that these large-scale, high-volume attacks end up passing usually within an hour. However, these attacks can damage software and infrastructure while also causing substantial monetary losses and reputation damage, all consequences that are hard to recover from.
Myth #2: Only large organisations are targeted by DDoS attackers
DDoS attackers target businesses of all sizes and sectors. Sometimes, competitors launch attacks against one another, or a malicious actor will bring down a smaller website knowing it will wipe out the entire server. Although attacks against big companies like Google make the headlines, DDoS attacks can actually have a profound impact on small- and medium-sized businesses, which are three times more likely to be targeted by cybercrime than their larger counterparts.
Myth #3: DDoS attacks are no longer a challenge
DDoS attacks are not only on the rise but also increasing in complexity, with as many as 38 different attack vectors involved in recent attacks. The latest botnets use fewer devices as each infected computer is significantly stronger with cloud computing power. High-performance botnets can be up to 5,000 times stronger than traditional ones, giving them the power to breach virtual private servers and access management consoles using leaked credentials.
DDoS attacks, more aggressive than ever: How can companies protect themselves?
While DDoS attacks are predicted to rise in 2023 and beyond, organisations can take steps to protect themselves by having the right measures in place to prevent and mitigate these attacks. DDoS attacks come in several types and are quite complex to detect, requiring an equally complex response that coordinates several measures that include – but are not limited to – rate-limiting, IP filtering, geo-blocking, firewalls, and a robust incident response plan.
Although technical measures are key to success in DDoS prevention, we should not forget an equally important resource – employees. Boosting your team’s awareness and understanding of cyber security is a solid step toward strengthening your organisation’s defences against any type of cyber threat. This is where SoSafe steps in, providing gamified learning modules and awareness training that empower your employees to avoid falling into the hackers’ clutches. Your workforce will be equipped to protect themselves and your organisation from several threats like malware, which is often the initial breach point for hackers looking to build botnets. By evading these botnets, they act as guardians for your business, keeping cyber threats at bay and your internal servers secure.



















