
Spoofing
What is spoofing?
In cyber security, spoofing is a tactic where perpetrators hide their identity or impersonate others. This deception allows cybercriminals to conduct detrimental acts like unauthorized wire transfers, circumventing security, breaking into company systems, or misappropriating classified data, typically by impersonating trusted figures to manipulate their victims.
Spoofing, phishing, and social engineering share common ground. Specifically, cybercriminals use spoofing techniques in phishing emails to hide the sender’s identity and emotionally manipulate their victims. This scenario played out in 2022 with a series of scams under the guise of PayPal. Deceptive requests for PayPal payments were made, and spoofing methods were used in phishing emails and calls to mimic PayPal. The end goal was to extract victims’ information for more targeted spear-phishing attacks while keeping their sinister intent under wraps.
When spoofing, cybercriminals use a wide range of techniques and means to pose as someone else, including e-mail addresses, telephone numbers, IP addresses, GPS, URLs, and text messages. We’ll talk more about spoofing types later, but first, let’s look at what they have in common and the approach cybercriminals usually take.

How does spoofing work?
Spoofing usually follows a similar pattern: Cybercriminals select a channel of attack and use various means of deception to pose as an individual or organisation the victim trusts. Sometimes, these attacks start with a successful phishing or spear-phishing attack. If the criminals can access personal information, they may then be able to use spoofing to perform further attacks under a false identity.
Next, the criminals try to get their victims to perform an action, usually through emotional manipulation: They pressure their victims, take advantage of their fear or curiosity, or induce other emotions to get them to do as they please. As a result, most spoofing attacks constitute a form of social engineering where the emotional manipulation of victims is at the forefront.
The exact goals of spoofing attacks vary depending on the attack type. In most cases, the primary objective is to steal someone’s identity. Other times, cybercriminals use spoofing to remain anonymous during their attacks, only seeking to conceal their own identity. Both identity theft and identity concealment help them engage in deception, take advantage of trust, and conduct sophisticated phishing, social engineering, and DDoS attacks. Spoofing is generally only part of a larger attack where cybercriminals try to enrich themselves or harm others.

Difference between spoofing and phishing
The line between spoofing and phishing is fluid, especially as many phishing attacks involve spoofing, but not all spoofing attacks are phishing. While spoofing refers to a type of deception, phishing is a specific attack tactic with the intent of causing harm.
The term “spoofing”, at its core, merely refers to the provision of false information. Attackers use different techniques to make their victims believe that the attackers are someone else so that they can take advantage of their victims’ trust.
On the other hand, phishing is a specific cyberattack type where cybercriminals try to steal access credentials, bank information, or other sensitive data, often via email. But there are phishing types that are conducted outside of emails, such as vishing (telephone), smishing (text message), and quishing (QR code). Cybercriminals may use spoofing methods to gain their victims’ trust – such as by directing them to a website with a spoofed URL – as part of these phishing attacks.
Is spoofing illegal?
Spoofing itself isn’t illegal in its initial stages because it starts out as simply the presentation of false information. Depending on a country’s or region’s jurisprudence, certain spoofing types are illegal when used for malicious intent.
Illegal spoofing types include IP spoofing and caller ID spoofing, where cybercriminals commit identity theft and use methods that aim to give them access to their victims’ sensitive information. Such deception is a crime and can be prosecuted in court, with punishment ranging from fines to imprisonment.
Spoofing is legal in other cases, such as when the concealment of facts serves to protect an individual. The most drastic example is the witness protection programme. Spoofing methods are also used for legal purposes in cyber security, such as for ethical hacking, penetration testing, and phishing simulations. These are used to identify vulnerabilities and improve security measures.
Successful and scalable: Why criminals use spoofing
Because many cyberattack methods involve spoofing, it’s difficult to assess the scope of it in numbers. What is certain, however, is that spoofing is a fixture in a cybercriminal’s arsenal and will become more popular as technology advances. AI tools like VALL-E are already making it possible for cybercriminals to imitate speech and individuals’ voices in seconds. This not only makes it easier for cybercriminals to conduct various spoofing methods but will also make them much more convincing and dangerous for the victims.
As social engineering attacks that involve spoofing become increasingly successful, the global cost of cybercrime will explode. From 2022 to 2023, damage caused by cybercrime is reported to have increased from 8.44 to 11.5 billion USD, equal to a 36 percent increase. By 2027, costs are expected to increase to 24 billion USD, three times higher than in 2022. According to the Verizon Data Breach Investigations Report 2023, about 74 percent of all cybercrimes start with a human factor. This means social engineering and spoofing are extraordinarily profitable for cybercriminals – and pose an immense risk to companies.
What are the different spoofing types?
Cybercriminals use different spoofing methods and channels to take on a new identity:
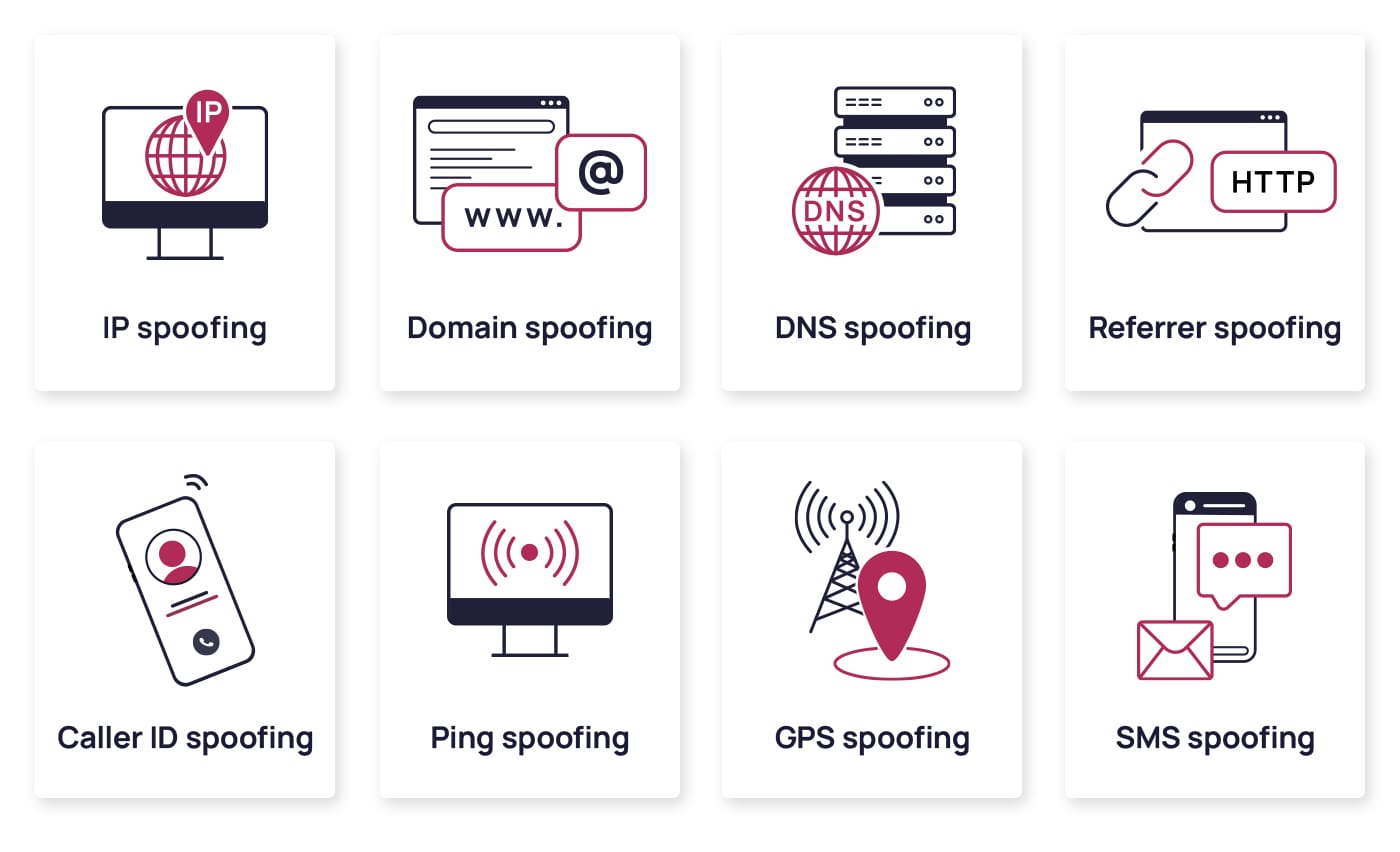
IP spoofing
Every device compatible with the web connects to the Internet through an Internet Protocol (IP) address. This unique sequence of numbers is a distinct identifier, marking the device’s specific location in the digital space. However, a technique known as IP spoofing throws a wrench into this straightforward system. In IP spoofing, attackers manipulate source IP addresses in created IP packets to mask their own address or mimic another system or device, adding a complex layer of deception to online communications.
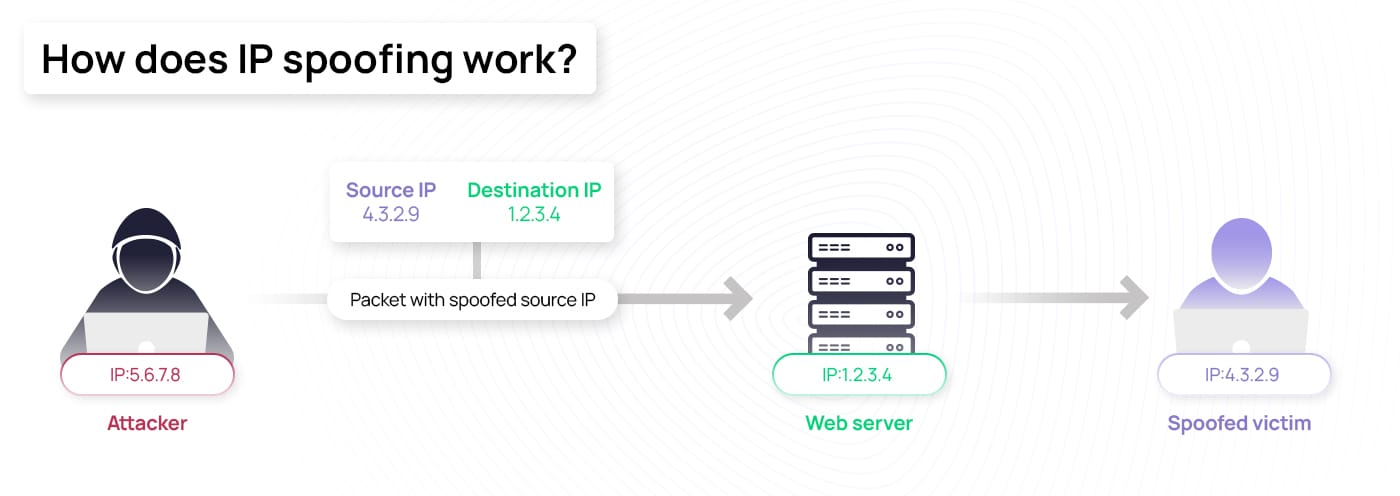
In many cases, cybercriminals spoof IP addresses to circumvent firewalls or blocklists. This can be especially harmful to companies without additional authentication measures if the IP address is not identified as dangerous. Once criminals have access to internal data and systems, the potential for damage is immense. IP spoofing is frequently used for Distributed Denial of Service (DDoS) and man-in-the-middle attacks to target individual devices or entire networks. In these situations, the attackers use IP spoofing to overwhelm systems or infiltrate a communication process unnoticed, giving them access to information.
Domain spoofing
Every day, we interact with websites, URLs, and email addresses, assuming they are legitimate. However, a technique known as domain spoofing challenges this trust. In domain spoofing, authentic-seeming websites, URLs, or email addresses are created to appear identical to the real ones. There are two primary forms: website and URL spoofing and email spoofing.
Website and URL spoofing involves cybercriminals creating a near-identical copy of a trusted website or URL. The goal is to encourage users to interact with the counterfeit site and possibly enter sensitive information. These fake domains are usually designed with minor changes that can be easily confused with the original ones, making the deception hard to detect.
In the case of email spoofing, the trickery takes a different shape. Fraudsters impersonate a familiar email address to make it seem as though the email is genuine. Subtle modifications, such as replacing the number 0 with the letter O, can easily go unnoticed due to the similarity in many fonts. The body of these emails typically includes phishing elements like harmful links or attachments. Because the sender’s address appears trustworthy, users may fail to recognise these malicious elements.
Referrer spoofing
In the vast world of online marketing and SEO, a valuable piece of information is the source from which visitors originate, often referred to as the referrer. It serves as a digital roadmap, guiding website owners to understand their user traffic patterns. This information is typically recorded in server logs, creating a digital paper trail of visitor footprints.
This process can be disrupted through a technique known as referrer spoofing, a variant of URL spoofing. The genuine referrer information is replaced with a bogus one during the forwarding of the HTTP request. This manipulation can muddy the digital paper trail, obscuring the true origins of the website traffic. Cybercriminals leverage this strategy to cover their tracks or sidestep authentication processes, making their activities harder to detect.
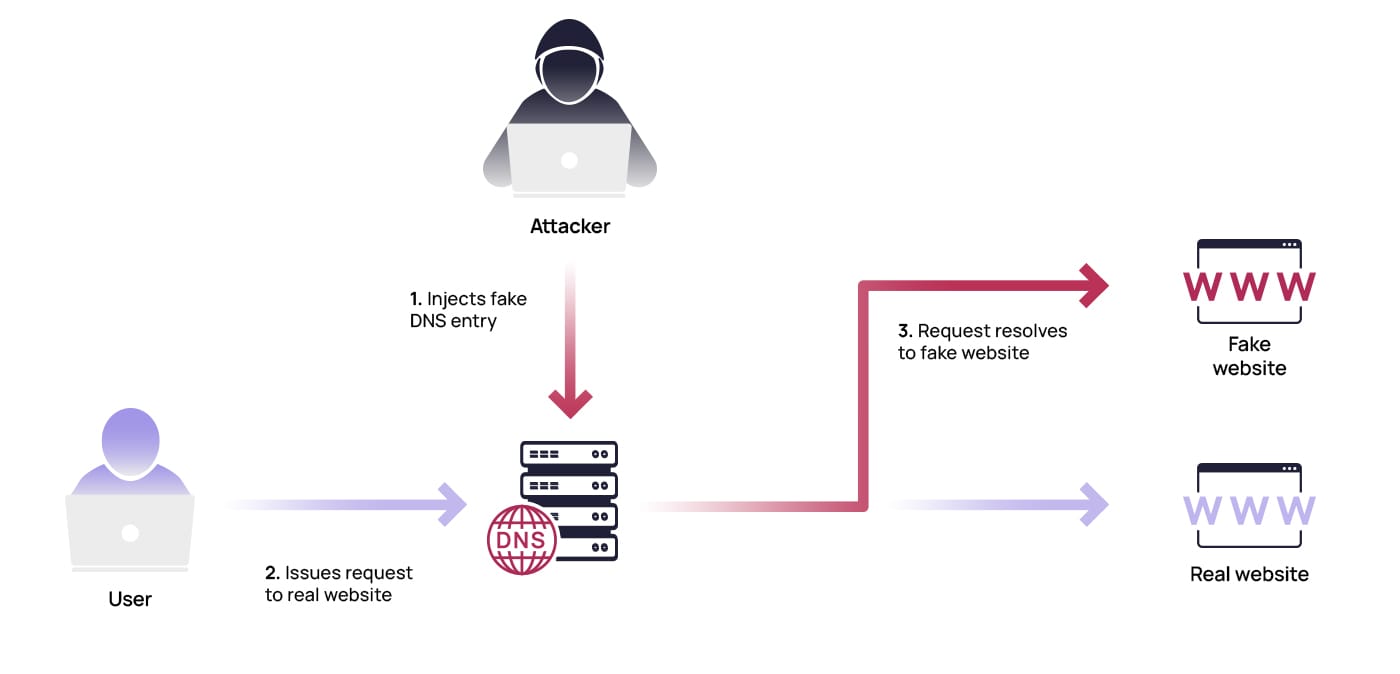
DNS spoofing
On the Internet, the Domain Name System (DNS) acts as an efficient directory, associating domains with their respective services. It’s like calling a friend on your phone and being connected to their specific number. When users input a domain, they’re seamlessly guided to the relevant website.
However, hackers have mastered a strategy known as DNS spoofing. This stealthy manipulation alters DNS entries, leading unsuspecting users to fraudulent websites, monitoring their activity, or deploying malware. This ploy is so interesting for threat actors because of its invisibility – victims are often completely oblivious to the intrusion.
A popular method within DNS spoofing is DNS cache poisoning. This involves tainting DNS entries within the resolver cache. As a result, the server displays a deceptive IP address to users, directing them to a dangerous facsimile of the intended website.
Caller ID spoofing
Cybercriminals may contact their victims over the phone in a method known as caller ID spoofing, also known as phone spoofing. The attackers hide their actual number and appear to be calling from a familiar number or genuine area code. They may use VoIP services that often allow users to select a name or number that will be displayed when they call. Because the attackers use a fake caller ID, the victims have no reason to be suspicious and accept the call, and then the attackers try to obtain the victims’ sensitive information, such as account credentials, personal information like date of birth and social security number, or even passwords. Caller ID spoofing is often a part of vishing attacks.
One caller ID spoofing type is voice spoofing, where the criminals imitate the voice of someone the victim is familiar with via voice recordings or other technology. As AI tools become more commonplace, this manipulation is becoming more widespread and easier to implement. In one very recent case, criminals tricked a mother in Arizona by playing an artificial imitation of her daughter screaming over the phone. She later discovered that her daughter was safe, but the mother said she never thought twice about whether the voice was genuine. Caution and a healthy dose of skepticism are key to identifying spoofed phone calls.
SMS spoofing
SMS spoofing is a deceptive strategy where the recipient receives a text message from an obscured or unidentifiable number. Drawing parallels with caller ID spoofing, the incoming text message is designed to appear as if it originates from a familiar entity, such as a friend or reputable company.
These cyber adversaries aim to elicit a response or coax the recipient into clicking a link embedded within the message. Such an act of smishing could inadvertently lead the user to download malicious software, opening a gateway for further security compromises.
Ping spoofing
Think of a ping as an IT health check, a diligent monitor tirelessly assessing the availability of a server or host. In the gaming world, it plays the role of a speedometer, measuring the stability and rapidity of your Internet connection – the swifter the connection, the lower the ping. However, in this digital landscape, deception can emerge in the form of ping spoofing. This is where gamers artificially alter their ping to carve out an unfair advantage over competitors. It’s a subtle form of deception, extremely challenging to detect and trace, adding another layer of complexity to the gaming world.
GPS spoofing
GPS spoofing represents a digital sleight of hand, where a device’s actual geographical coordinates are masked, leading to a misrepresented location. This subterfuge has found a home in online gaming, particularly in Pokémon GO. Players often employ this tactic, obscuring their true location to carve out an advantage over their gaming adversaries. Consequently, Niantic, the game’s developer, is preparing to tackle this deception more robustly.
However, the impact of GPS spoofing is not confined to the gaming world. It opens Pandora’s box of risks across various other applications and devices, offering an avenue for malicious entities to manipulate navigational systems in cars, airplanes, ships, drones, and public transportation systems.
Beyond the types mentioned above, cybercriminals’ toolkits encompass other disguise tactics like ARP spoofing and DNS hijacking. Regardless of the specific method employed, the essence of deceit remains constant and can potentially infiltrate any digital realm. As such, it’s crucial to remember that cybercriminals will continue to learn how to use new means of communication to evolve their repertoire of spoofing strategies.
Spoofing in action: A rundown of real-life attack scenarios
In recent years, cybercriminals have used various spoofing methods to get their hands on sensitive information. While they use spoofing to trick individuals, governments have also been known to hire criminals to engage in spoofing against other governments, global organisations, and companies. In 2018, the Russian military intelligence agency GRU hired seven Russian agents to conduct spoofing against the Organization for the Prohibition of Chemical Weapons (OPCW). The agents attempted to compromise login credentials and infiltrate accounts – but before they could succeed, they were discovered after sending spear-phishing emails and using proxy servers, malware, and fake personas.
When the global coronavirus pandemic began in March 2020, the World Health Organization (WHO) also fell victim to a spoofing attack. The attackers had activated a harmful website that copied the WHO’s internal email system, intending to steal WHO employees’ passwords and obtain sensitive information about COVID-19, such as information about tests, vaccinations, and treatments.
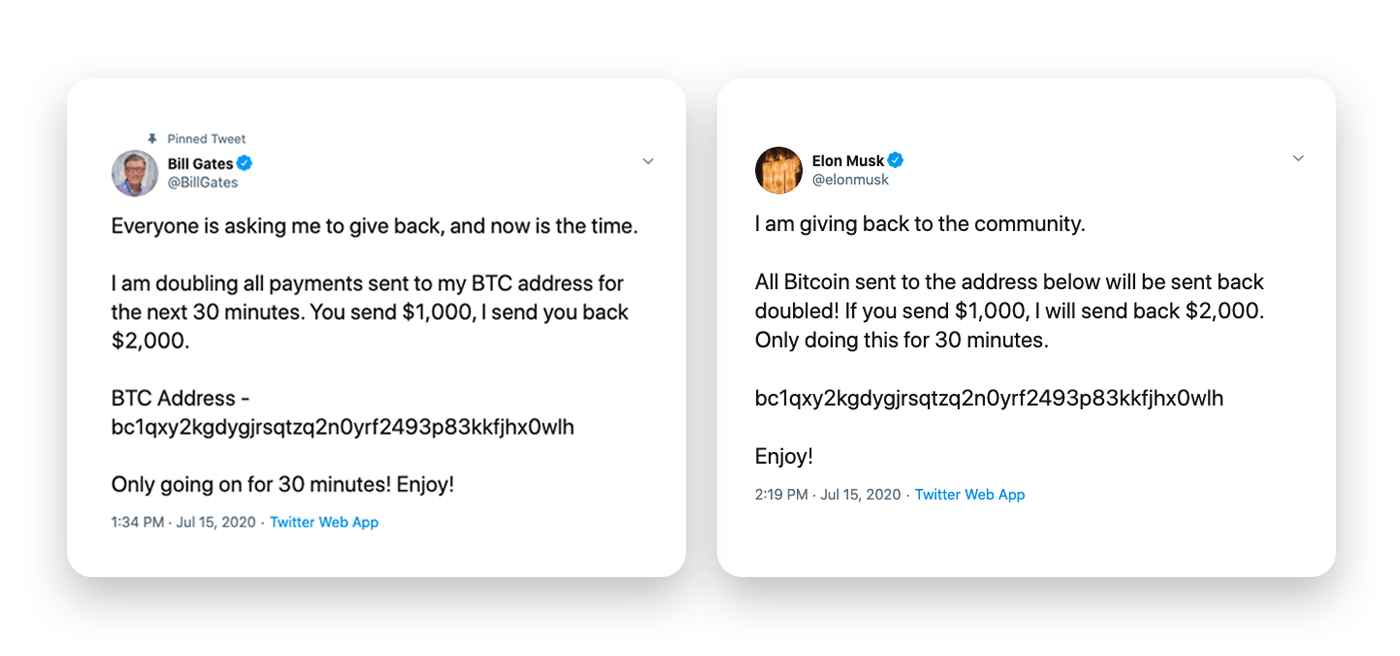
In the same year, one major attack against Twitter allowed multiple cybercriminals to take over prominent users’ accounts to advertise for investments in cryptocurrency, posing as celebrities to request transfers of Bitcoin. The attackers used social engineering tactics against Twitter employees and spoofing methods, gaining over $100,000. This attack triggered discussions about the social media platform’s own security measures.
How to identify a spoofing attack?
Identifying spoofing isn’t always easy, but there are a few trademarks you can note to determine whether cybercriminals are trying to deceive you.
To quickly detect possible spoofing, consider these key signs:
- Reason for contact: No matter how you are contacted – email, text message, or phone call – are you being reached about an issue you’re already aware of, or are you being contacted out of the blue? If it’s the latter, be especially cautious.
- Confidential information: Never disclose sensitive information, such as account information, social security number, or identification, to third parties without being absolutely sure of their identity.
- Emotional pressure: Sometimes, attackers place emotional pressure on their victims by emphasizing the supposed urgency of the matter or placing them in a stressful situation. This is a typical sign of a social engineering attack.
- Hyperlinks: Do the domains of the links within the message differ from the sender domain? Ensure that the website you want to visit is genuine, such as by manually entering the URL into the address bar.
- Security protocol: Check if hyperlinks contain HTTP instead of the secure communication protocol HTTPS. This could be a sign of fraud.
- Display name and discrepancies: Make sure the display name corresponds to the address and has not been spoofed. When in doubt, contact the supposed sender of the email by other means, and type the correct URL into your browser if you receive a link. Read our blog post to learn more about how you can identify email spoofing and phishing.
- Security frameworks: There are ways to identify and filter out fraud in most conventional email programmes. These include Sender Policy Frameworks (SPF), which compare IP addresses with email domains to prevent spam and spoofing; DomainKeys Identified Mail (DKIM), which uses digital signatures to ensure that emails are not manipulated between the sending and receiving servers; and Domain-based Message Authentication, Reporting, and Conformance (DMARC), which shows the recipient that the email is secured with SPF and DKIM. Usually, these options are displayed in your email programme or for specific emails.
Outsmarting spoofers: Effective techniques for prevention
As we delve deeper into the digital age, the threat of spoofing rises, emphasizing the need to secure our online presence. Let’s explore a set of protective measures that play a significant role in warding off spoofing attacks:
- Secure your accounts: Use multi-factor authentication when available, and ensure you use robust passwords. These steps also help prevent attackers from leveraging phished data for further phishing and spoofing attacks.
- Be careful about what you share online: Guard your personal data and be discerning with what you share online, particularly on social media. Publicly available information, voice clips, and photos can fuel cybercriminals’ spoofing attempts. Remember, your digital footprint can make it easier for them to impersonate you, potentially leading to severe consequences.
- Keep software and hardware up-to-date: Ensure your software and hardware are current and fortified with technical safeguards like antivirus programmes and email filters. These can help counter domain spoofing attempts and other threats, limiting the damage from potential successful attacks.
- Keep informed and remain cautious: Because spoofing is a social engineering tactic, staying alert is crucial to preventing it. Stay up-to-date on the latest cyberattack tactics and remain skeptical of online activities that seem suspicious. Spoofing methods are always evolving, so the better informed you are of the current tactics, the easier it will be for you to identify them.
On guard against spoofing threats: How can you protect your organisation?
Spoofing isn’t confined to individuals – organisations are also common targets of wide-reaching social engineering attacks. As an integral part in the elabourate scheme of cyberattacks, spoofing enables the spreading of malware and ransomware. In the business world, this can lead to serious implications affecting an entire organisation.
The safety of companies and organisations depends on fortified technical security measures, a solid security infrastructure, regular system updates, and a keen awareness of current security threats. It’s crucial for every employee to stay informed about the latest trends in cybercrime to ward off deceptive attacks. Solutions that focus on compliance as well as continuous learning, such as SoSafe’s platform, are particularly effective. Through engaging, personalized cyber security awareness training, real-life spoofing and phishing simulations tailored to your employees’ needs and risk level, our platform helps nurture secure behaviour among employees and safeguard the organisation against damaging attacks.



















